This is another post in the unintended series about untangling your Azure account. My first post was about naming and grouping your Azure Resources. The second was about writing conventions and following them. This third post is about managing Azure Access Control.
Developers, Developers, Developers
There’s nothing inherently wrong with handing out developer access to each resource and resource group they need. You will have a mess of access rights spread all over, but you will easily revoke access by removing developers from the subscription.
If you need to manage privileges in a structured way, it is less than ideal. That is why I have developed a convention for managing access in our Azure subscription. It’s quite easy.
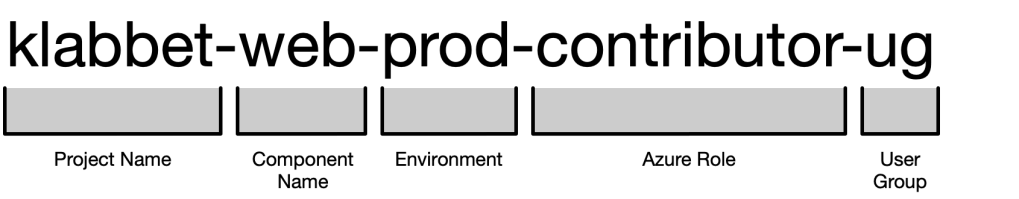
For each resource group, create one user group with contributor role, and use the following name format.
Let’s break it down
- Project Name and Component Name should be exactly the same as the resource group name.
- Environment, I usually go with
devandprod. I have never come across a situation where I needed to hand out access specifically totestorstage. Sodevmeansdev&testwhereprodmeansstage&prod. - Contributor is useful to have if you need to hand out access for more roles later. For me, the most common access role after contributor has been monitoring.
- UG is the user group suffix, which helps you deal with these in Azure API scenarios.
There will be one user group for every resource group.

Assigning Access
You can now assign access to the user groups instead of the Azure resources directly.
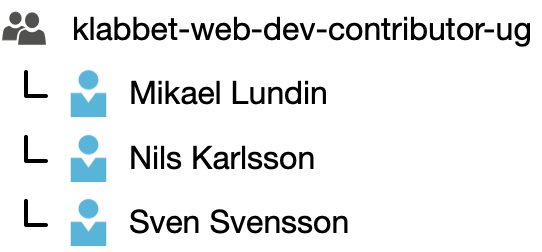
Managing access will become much easier.
Groups of Groups
Doing this will unlock the potential of combining user groups into larger user groups. If the project “Klabbet” has both a web and api component, we can create a user group that will give developers access to both.
| User Group | Member Of | Comment |
| klabbet-dev-contributor-ug | klabbet-web-dev-contributor-ug klabbet-api-dev-contributor-ug | API and Web dev access. |
| klabbet-prod-contributor-ug | klabbet-web-prod-contributor-ug klabbet-api-prod-contributor-ug | API and Web prod access. |
By combining user groups into larger user groups we will get better control of what kind of access a user has, without investing too much effort.

Summary
I’ve presented you a format for access control that does not require much effort to setup, but provides lots of flexibility to take control of your access control.
If you’re interested in my convention for access control you can find the specification here.
- Klabbet wiki: Azure / Access Control
